Need a new dimension of security in motor control and power conversion?
The iC7 series lets intelligence set you free with drives that act as sensors, giving you access to more data. This freedom is underpinned by unique security-by-design, which increases your protection against cyber-attacks using a hardware crypto chip, protected firmware, and encrypted data transfers.
These security features in the drive or power converter make it easier for you to protect your systems and your data, giving you a secure component you can rely on.
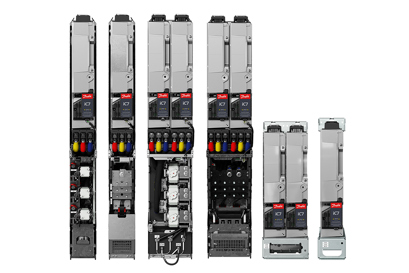
iC7 series: Secure-by-design drives and power converters
Cybersecurity is a fundamental architecture criterion of the iC7 series. Our secure-by-design drives and power converters incorporate security considerations into every stage of the product lifecycle, from initial concept and design through manufacturing, commissioning, and maintenance of the drive. This enables you to comply with the demands of today and tomorrow quickly, efficiently, and reliably.

World's most secure
The iC7 series is the first drive and power converter portfolio in the world offering a verifiably secure and tamper-proof operational environment. The difference is its design for hardware-based security, which underpins every security feature of the iC7 series:
- Network connectivity: Communication between the drive and the MyDrive® Insight commissioning tool is end-to-end encrypted by using TLS/SSL cryptographic protocols as used by HTTPS in web browsers
- Tamper-proof hardware: Prevents unauthorized alteration and protection against physical and side-channel attacks
- Trusted firmware: Firmware and applications are encrypted and only executed if they are genuine
- Public key certificates: Provides stronger authentication and secure device identification
Protect your digital systems
The iC7 products can collect an enormous amount of raw and processed data. Use these data to optimize your productivity and maintenance procedures, and to extend machine or installation lifetime. To add value to your operations, you can communicate these data via the automation network or the cloud, for further analysis and actions. When communicating data, of course data security is a priority. The risk of a security breach is often a concern and can even be a showstopper. Ensuring secure communication is not only important in IT, but also essential for well-functioning Industrial Internet of Things. The iC7 series takes this barrier away with integrated cybersecure hardware for the highest possible protection against unauthorized access.

Fulfill your cybersecurity compliance obligations
As a system integrator or OEM, you may be obliged to demonstrate that your system is capable of achieving the intended security level for different parts of the system. Our user guides are developed to provide up-to-date recommendations for system integrators using Danfoss drives and power converters as components.

Cybersecurity begins with your suppliers
At Danfoss Drives, we take the responsibility of cybersecurity and cybersecure component supply seriously. We strive to ensure the most up-to-date protection against unauthorized access, for our customers. This is why our product development processes are certified for high cybersecurity, ensuring optimal design of the iC7 series drives and power converters manufactured in our factories. This commitment reflects our dedication to cybersecurity matching the highest standards in the field.
For more insights into security levels for mandatory compliance:

Let Danfoss Drives power your development

Regardless of the industry you operate in, using fully versatile drives will make all the difference. Reliable drives designed to give you superior motor control and predictive maintenance capabilities, and with built-in encryption. For the highest-performing systems possible.