Danfoss Electronic Controllers is following secure development towards IEC-62443 in their Development Teams
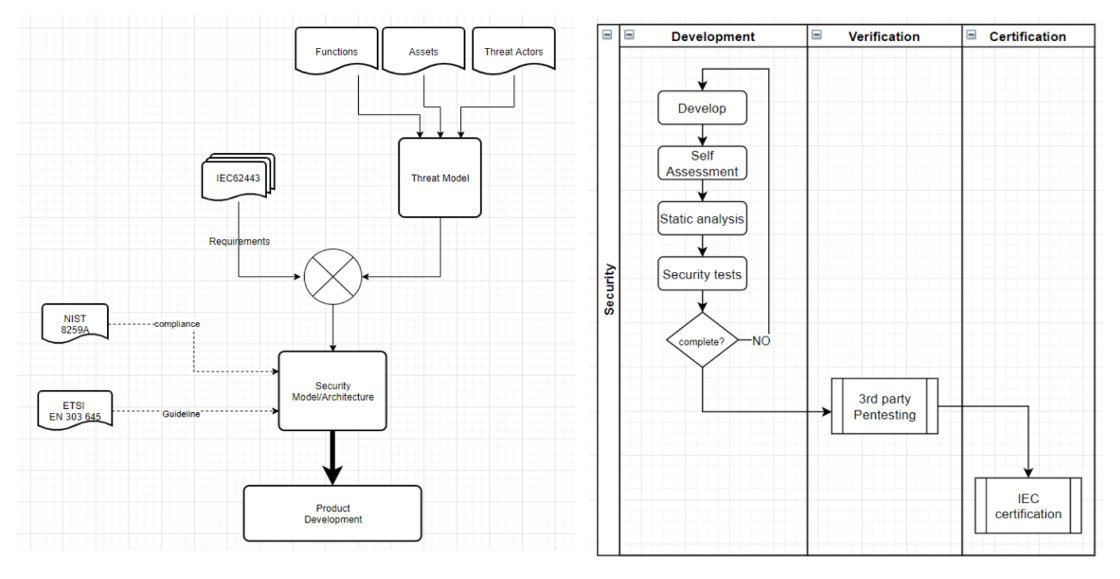
Secure development process
Recommendations for Customers
To help keeping your Danfoss products secure and protected, we recommend that you implement below cybersecurity best practices.
Following these recommendations may help significantly reduce your company’s cybersecurity risk.
Common Security Terms:
CVE:
Short for Common Vulnerabilities and Exposures, is a list of publicly disclosed computer security flaws.
DDOS:
Distributed Denial of Service: this term is used when 100 000s of remote devices attack a single device on the net web. This is a highly effective attack on a system. Not even large corporations and security organizations can maintain operations during such attacks. These attacks have been measured to include 400+ Terabits/second attack rates, which simply floods out the connection to the device. This cannot be mitigated at any level at other than the internet backbone.
There is no cheap defence against these kinds of attacks and the only effective way of mitigating these attacks is to avoid them, by hiding.
Remote Exploit:
One can assume that all software that faces the internet will contain exploits. Therefore, researchers are continually searching for these, and when found, the software providers create patches that mitigate the exploit. It is therefore extremely important to update software and keep it updated with the latest versions to prevent vulnerabilities in the system.
For example older Systems Managers used the 1.12.1 version of Nginx, where several vulnerabilities were discovered, and patched, thus the newest System Manager version 3.1.9 now uses the 1.21.0 version of Nginx, which currently has no known vulnerabilities. Therefore, it is important to upgrade to the latest Danfoss release – the release numbers may have increased after the writing of this document because new exploits are continually discovered.
General recommendations
- Devices should always be fully updated to the latest available software versions, issued by Danfoss. In every newer version, there might be some security updates, which are explained in the appendix.
- Ensure that the device is always protected from direct internet exposure. (Install network devices behind a firewall)
Danfoss strongly recommends protecting any network devices with a firewall and secure remote access principles.
The problem that may be experienced is that systems that are not fully updated may contain known remote exploits, that can have negative effects on the system. Known exploits are often published in the CVE databases, and on many security research sites.
This means that mapping the devices directly out on the internet is not recommended, but if it is necessary, it is important to use several safeguards to protect the system from direct internet access.
The general concerns for the devices are.
- DDOS – no software patches can protect against this kind of attack. (Thus, firewall protection is necessary)
- Known remote executions can allow an attacker to enter the device, therefore all software upgrades are necessary to remove known exploits.
- The exploiting of various known and unknown security vulnerabilities can cause system downtime.
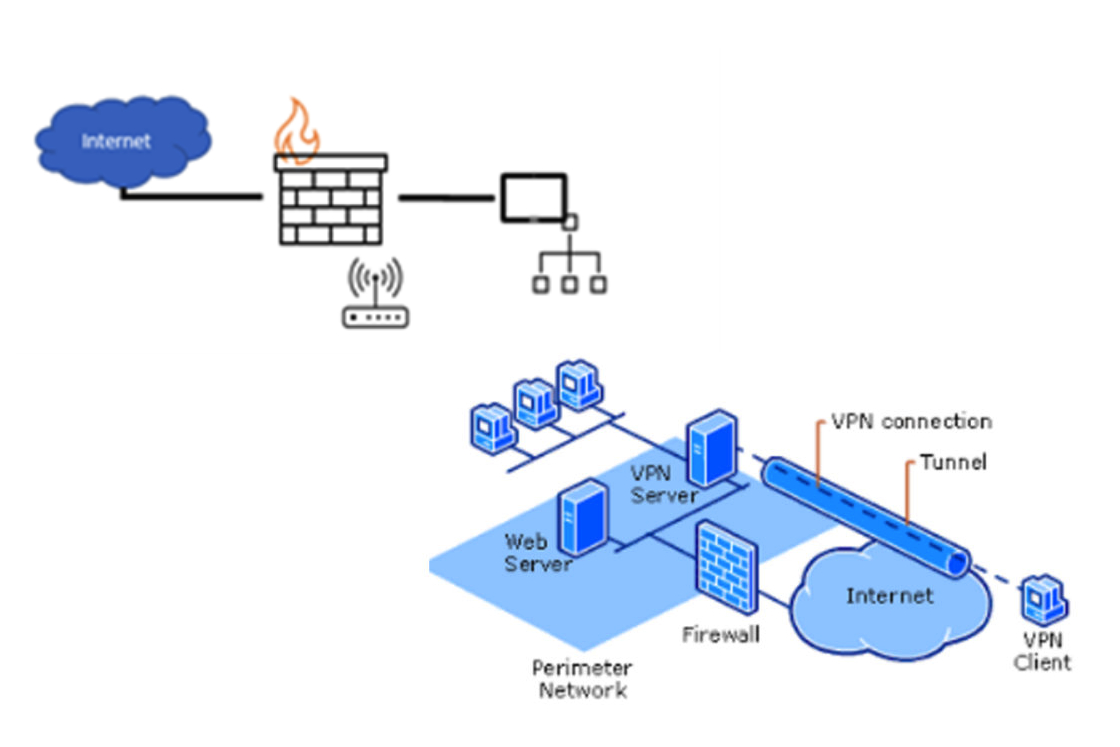
Break down system into network zones
Start to split your network into zones/segments. To have Danfoss devices placed on a separate network will reduce the attack surface.
This is in general a practice to consider in your network, independently of which devices you use.
The segmentation could even be extended to micro segmentation, so in case, one device is compromised, it will not spread to the rest of the network.
See below typical Segmented Network example:

Set up firewalls
Always place Danfoss systems and devices behind firewalls and other security protection appliances that limit access to only authorized remote connections. Building a highly protected network that helps prevent outside access is the most critical line of defence against cyberattacks.
We recommend that you follow these guidelines:
- Limit access to the networks on which Danfoss devices are placed.
- Ensure that Danfoss systems and devices are not accessible from the internet, unless placed behind firewalls and other security protection appliances.
- Restrict external network connectivity to your systems and devices.
- Continually monitor for events that might indicate attempted unauthorized access.
- Limit access to internal networks where devices reside.
- Isolate control and safety system networks and remote devices from the business network.
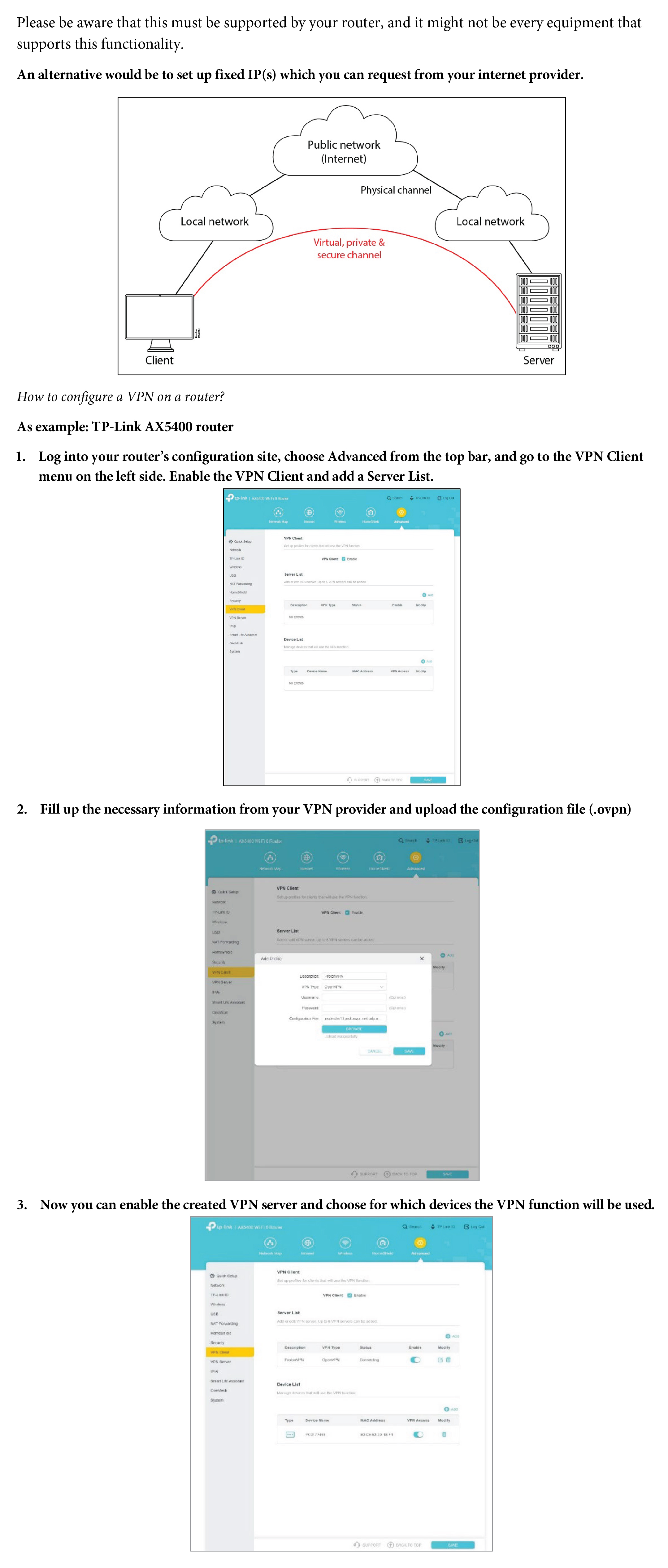
For a secure connection/access you can also use a VPN connection.
Use secure remote access methods
Implement secure methods for remote users to access your network. Require all remote users to connect and authenticate through a single, managed interface before conducting software upgrades, maintenance, and other system support activities.
When there is a need for accessing devices from remote locations it is important that the exposure of the device is limited as much as possible. The following solutions present ways of protecting the device and network while providing the flexibility to access the device, remotely.
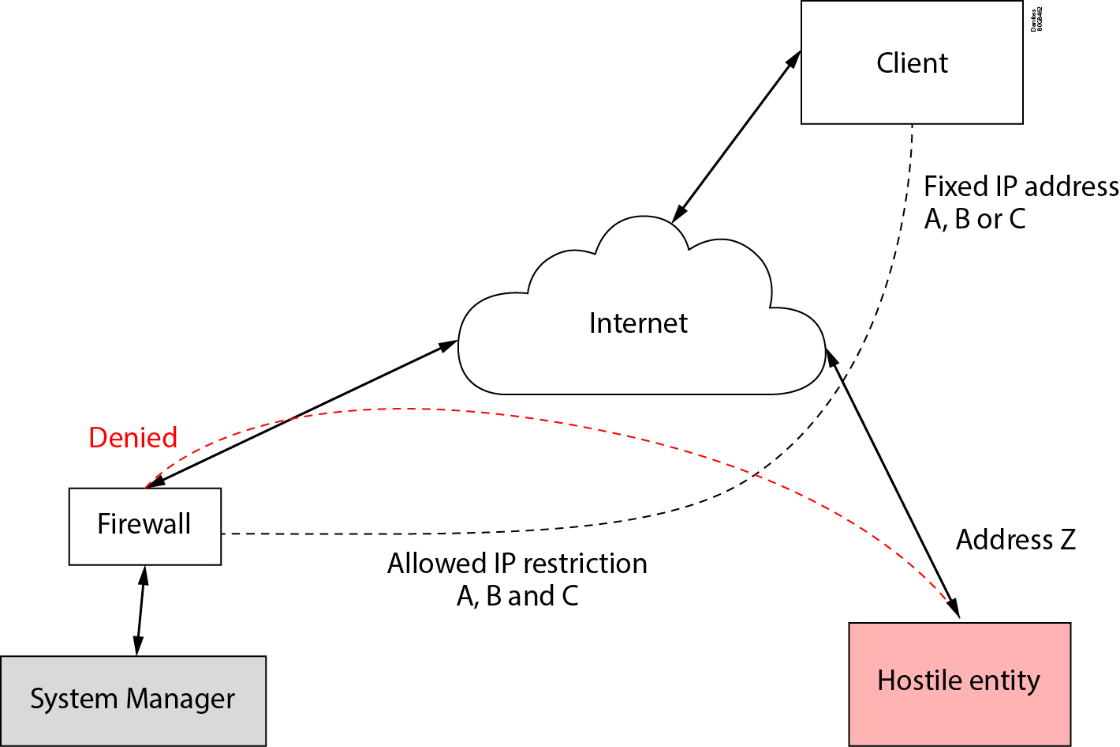
Fixed IP on the mobile devices:
Using fixed IP addresses on remote mobile devices is the simplest solution to maintaining remote access to the system while maintaining full security of the device against hostile attacks - it also protects the device against DDOS attacks.
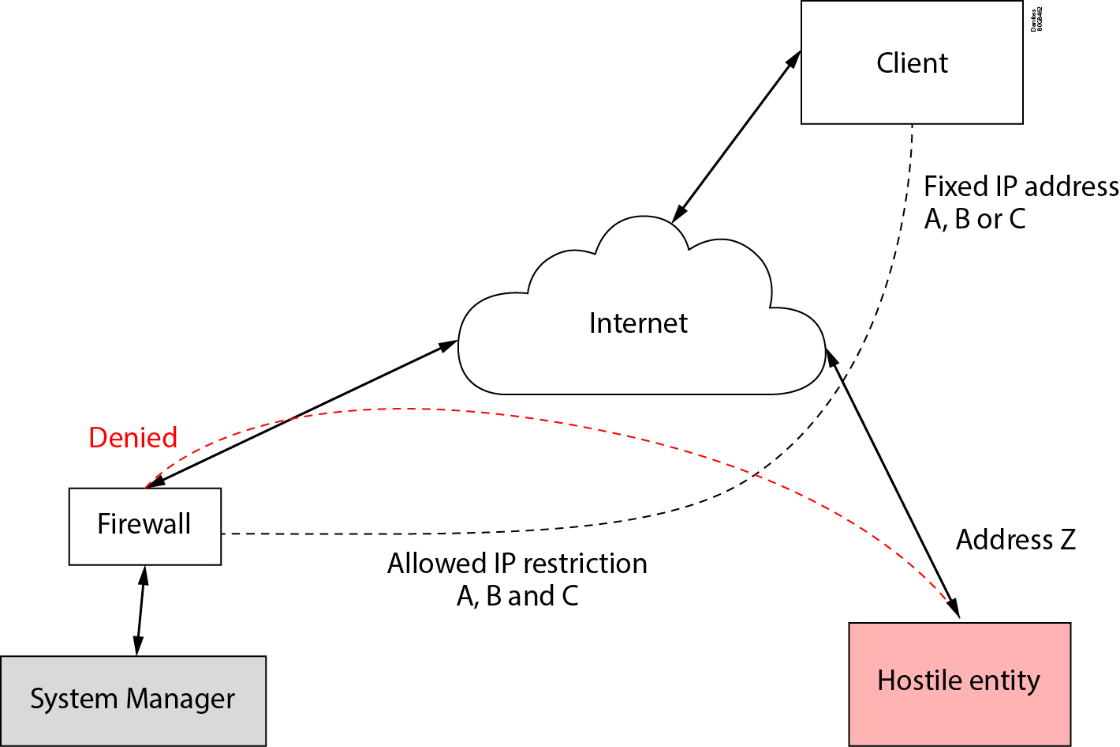
Proxy solutions
Proxy solutions are more complex to set up; however, they offer greater security as well as the ability to provide a proper valid SSL (Secure Sockets Layer) certificate for access to the system. The proxy system exposes an authenticated system access to the internet, and this authenticated access will take the worst part of any system attacks, protecting the System Manager from being compromised.
The proxy can use methods such as authenticators, 2-factor authentication, and other security mechanisms to make sure that only authorized access is allowed.
The proxy is IP locked to the firewall that is protecting the System manager, and all mobile clients, use random IP addresses, and authenticate to the proxy (usually using certificates, 2-factor authentication, or the like), creating a strong validation of the client.
All hostile clients are denied direct access by the firewall and the proxy as it cannot supply the required credentials to talk to the proxy.
This means that the proxy will endure most of all security attacks, and in the worst case the proxy will be DDOS and local access to the system manager is still possible.
Alsense Proxy solution
Alsense can provide this solution via a VPN (Virtual Private Network) based connection, or via an IP-bound proxy solution, where the connection can be limited to the Alsense cloud system - again minimizing the exposure of the system to the internet, allowing Alsense to provide the system protection.
Alsense is a Danfoss cloud solution for accessing System Managers, and much more. This solution provides the same as the proxy solution, however, it is managed by Danfoss, and as such does not need the client to implement, nor maintain and operate the proxy.
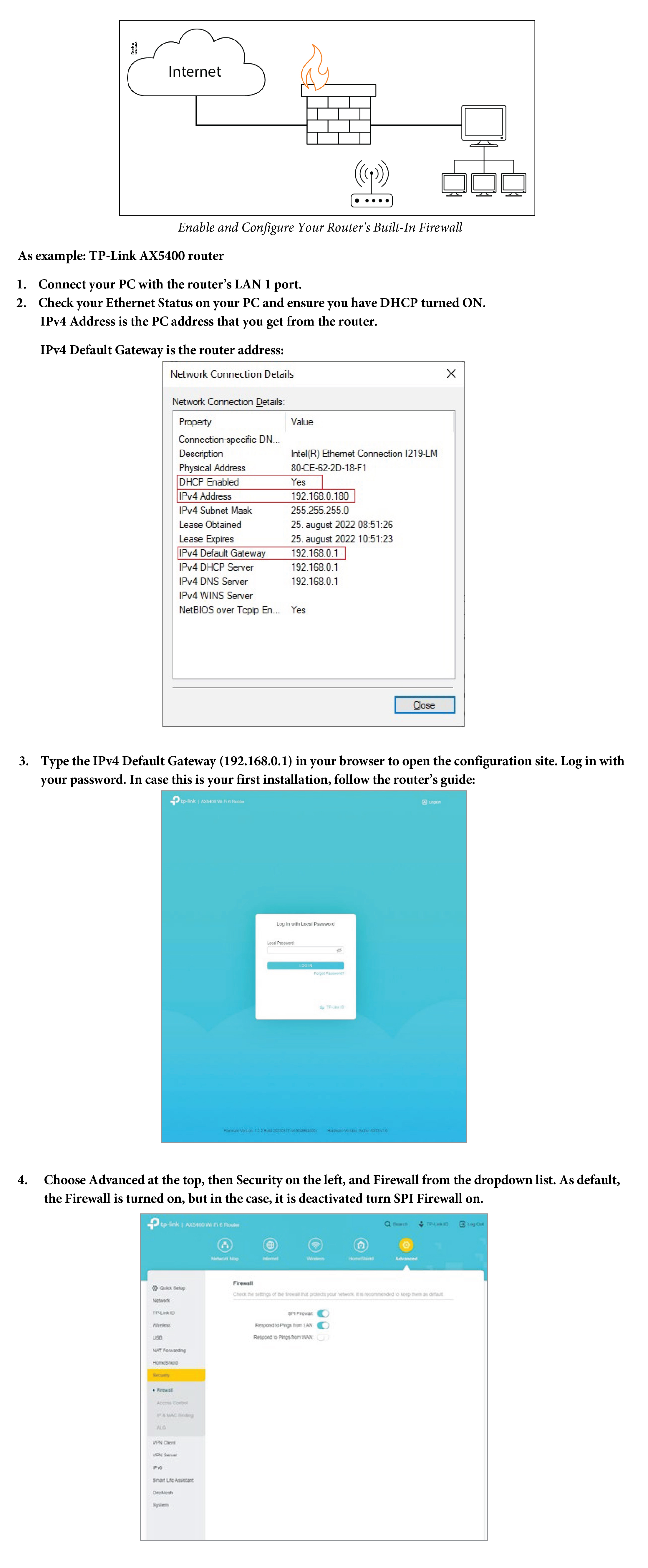
Technical Instruction & explanation for setting up a firewall
Technical Instruction & Explanation for setting up a VPN
Set up measures for detecting data breaches and incidents
Access to industrial networks, should be performed via authentication/audit logs, e.g., VPN or firewalls, so that access can be audited, and thus security events can be investigated if one occurs. Minimize the chances of data breaches by monitoring and auditing system events 24/7. Use intrusion detection systems, intrusion prevention systems, antivirus software, and usage logs to detect data breaches or incidents in their earliest stages.
As a good practice we suggest the use of networking monitoring software for any unusual traffic alerts, unsuccessful access attempts etc. Guidelines are vast right from general IT requirements covered in ISO 27001 to specifics in IEC 62443 and can be found in these international Standards.
|
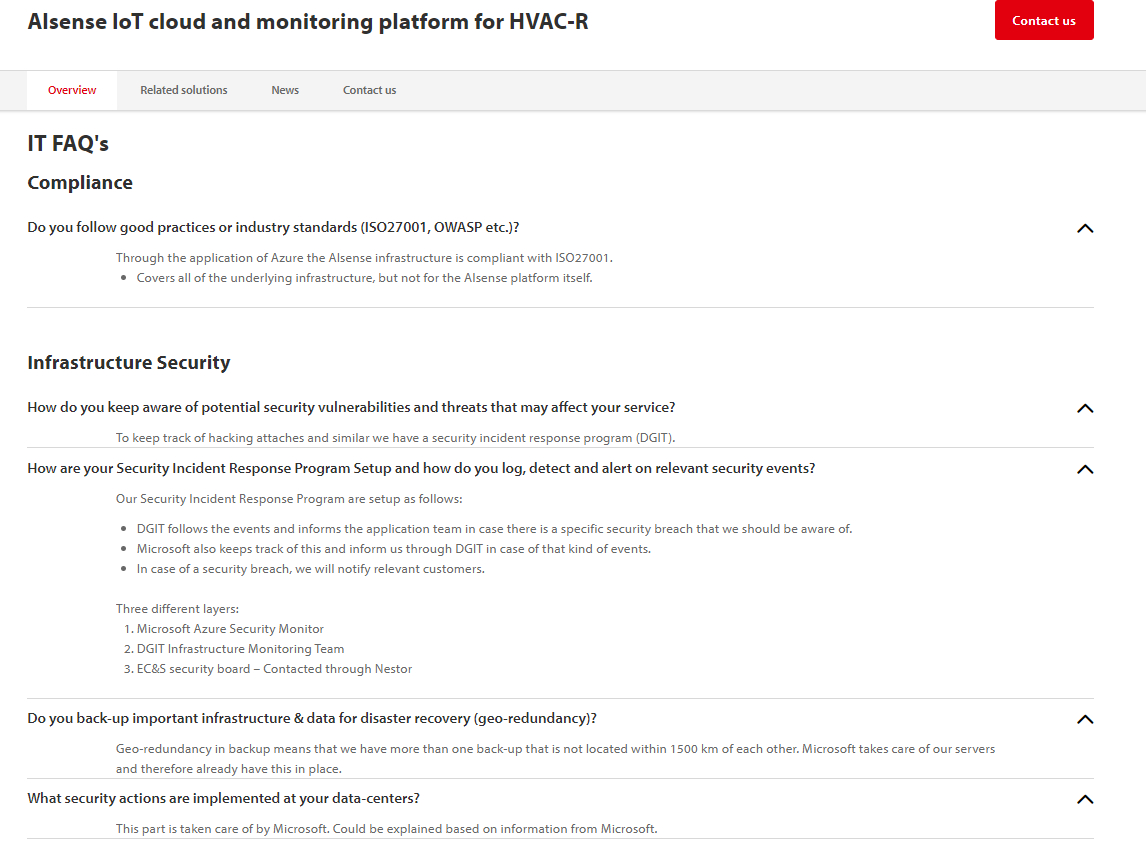
You can read more about Danfoss’ offerings related to monitoring solutions in the following link. Our Alsense Cloud solution already complies with OWASP, NIST and of course with General Data Protection Regulation: Alsense | IoT application for food retail and supermarkets | Danfoss | Danfoss |
Implement strong access controls
A plant or machinery is usually operated by more than one person, so central user administration is therefore recommended.
Change default passwords at commissioning and use the product to create user access levels.
| As an example: The Danfoss System Manager is a possible product, where you can define the user access level on the device to other possible users. |
This is particularly important for administrator accounts and control system devices. Use role-based access with multifactor authentication to help prevent security breaches and provide a log of access activity.
Users should avoid sharing passwords, as this can help with auditing of access, and prevents passwords from being leaked out to the population in general. A shared password usually ends up being known by everyone and prevents auditing of security issues.
Consider adding password security features, such as an account lockout that activates when too many incorrect passwords are entered.

Add whitelisting
Basics:
-
Whitelisting mechanisms provide additional protection against undesired applications or malware, as well as unauthorized changes to installed applications.
-
Whitelisting software creates or contains a list of programs and applications that are allowed to run on the PC.
Use whitelisting to define what Apps, IPs etc. are allowed, as whitelisting is the strongest form of security control as it blocks attempts to by-pass it. However, if for any reason whitelisting is not a viable option, then if possible, implement a blacklist to block known security issues, but knowing that blacklists can be circumvented easily.
Set up blacklisting
Blacklisting is a basic access control mechanism that allows blocking unwanted elements (email addresses, users, passwords, URLs, IP addresses, domain names, file hashes, etc.), except those explicitly mentioned. Those items on the list are denied access.
Blacklisting can help prevent known viruses, spyware, Trojans, worms, and other kinds of malware from accessing your system.
Using Blacklisting and Whitelisting Together
Often, using blacklisting and whitelisting together is the ideal option. You can use different approaches at different levels of your infrastructure and even use both within the same level.
Many organizations use both blacklisting and whitelisting for different parts of their security strategies. For example, controlling access to a computer or an account using a password is whitelisting. Only those with the password are allowed access, and all others cannot get in. Many of those same organizations also run anti-malware programs that use a blacklist of known malware to block harmful programs.
Train your people
Provide cybersecurity training to your employees to help keep your organization secure. Explain phishing emails, infected attachments, malicious websites, and other methods that attack them directly.
| As example: Danfoss IT Department, compliant to ISO 27001, provides every year a mandatory online training to all employees, in order to train people and to understand how everyone from a company can contribute to cybersecurity. |
Install physical controls to help prevent unauthorized access
While this is not just a cybersecurity issue, it is important to put physical controls in place so that no unauthorized person can access your equipment. Keep all controllers in locked cabinets and limit access to any connected devices.

General Information
Cybersecurity can only be efficient when everybody contributes to making the installation system secure.
As shown in above visualization in the family of IEC-62443 standards, it will require a shared effort and activity since security is a shared responsibility. As product supplier Danfoss aims to comply with IEC 62443-4-1 & IEC 62443-4-2.
It will additionally require responsibility and mitigation from System Integrator and Asset Owner.
Check the documentation for product-specific information
Danfoss provides detailed information with every product. Review the product guides on the website or those that accompany your products to find cybersecurity recommendations and best practices directly related to your Danfoss products.
|
Check also online specific information like the Danfoss FAQ page, where this best practice guide was placed. |
For additional information on cybersecurity best practices, review these resources:
- Quick Start Guide: An Overview of the ISA/IEC 62443 Series of Standards
ISA Global Cybersecurity Alliance (ISAGCA) - Cybersecurity Best Practices
Center for Internet Security - IEC 62443 Security for Industrial Automation and Control Systems
International Society of Automation (ISA)
Disclaimer:
THIS DOCUMENT IS INTENDED TO HELP PROVIDE GENERAL SECURITY RECOMMENDATIONS AND IS PROVIDED ON AN “AS-IS” BASIS WITHOUT WARRANTY OF ANY KIND. DANFOSS DISCLAIMS ALL WARRANTIES, EITHER EXPRESS OR IMPLIED, INCLUDING WARRANTIES OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE. IN NO EVENT SHALL DANFOSS BE LIABLE FOR ANY DAMAGES WHATSOEVER INCLUDING DIRECT, INDIRECT, INCIDENTAL, CONSEQUENTIAL, LOSS OF BUSINESS PROFITS OR SPECIAL DAMAGES, EVEN IF DANFOSS HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. THE USE OF THIS DOCUMENT, INFORMATION CONTAINED HEREIN, OR MATERIALS LINKED TO IT ARE AT YOUR OWN RISK. DANFOSS RESERVES THE RIGHT TO UPDATE OR CHANGE THIS DOCUMENT AT ANY TIME AND IN ITS SOLE DISCRETION.